Write up experiments and research with LaTeX templates for project and lab reports—including layout guidelines to help guide you through the writing process.
最近的

In this work, we investigate the STO as a detector with in-plane geometry using field modulation Spin Torque ferromagnetic resonance (FM-STFMR), during which microwave signal is injected into the device and output response is measured in terms of RMS voltage across lock-in amplifier. The microwave signal injected externally to STO, efficiently synchronizes signal at two times the frequency of free oscillation of the nanomagnet (f0). The synchronization efficiently enhances signal sensitivity at 2f0 which opens other potential for development of spintronic devices. The effect of synchronization in STO under applied input RF power follows a consistent decrease in sensitivity with increasing power. Better synchronization at 2f0 is noticed above threshold current and shows good agreement with the results of numerical simulations.
An indoor positioning system relying on time difference of arrival measurements of ultrasonic pings from fixed transmitters. Code available at https://github.com/YingVictor/ultrasonic-positioning
En esta práctica se utilizarán conocimientos de cinemática para encontrar el valor de la aceleración gravitacional, por medio de dos experimentos diferentes, uno que involucra la caída libre y el otro involucra un péndulo, además, se estimará la confianza y validez de los resultados.
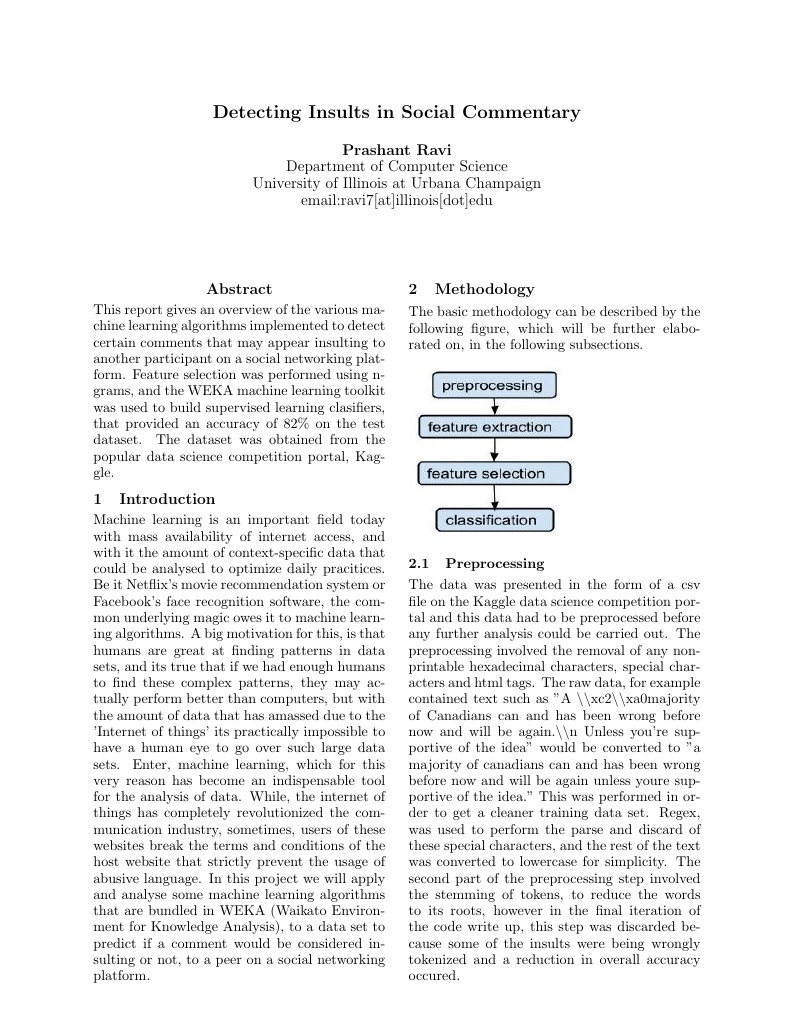
This report gives an overview of the various machine learning algorithms implemented to detect certain comments that may appear insulting to another participant on a social networking platform. Feature selection was performed using n-grams, and the WEKA machine learning toolkit was used to build supervised learning clasifiers, that provided an accuracy of 82% on the test dataset. The dataset was obtained from the popular data science competition portal, Kaggle.