Overleaf 模板库社区文章 — Recent
论文、演示文稿、报告等,以 LaTeX 编写并由我们的社区发布。

This research paper aims at exploiting efficient ways of implementing the N-Body problem. The N-Body problem, in the field of physics, predicts the movements and planets and their gravitational interactions. In this paper, the efficient execution of heavy computational work through usage of different cores in CPU and GPU is looked into; achieved by integrating the OpenMP parallelization API and the Nvidia CUDA into the code. The paper also aims at performance analysis of various algorithms used to solve the same problem. This research not only aids as an alternative to complex simulations but also for bigger data that requires work distribution and computationally expensive procedures.
Tutorial and Exercise for Cornell University chapter of Bridges to Prosperity. Adapted from the AguaClara Overleaf and LaTeX Tutorial written by William Pennock.
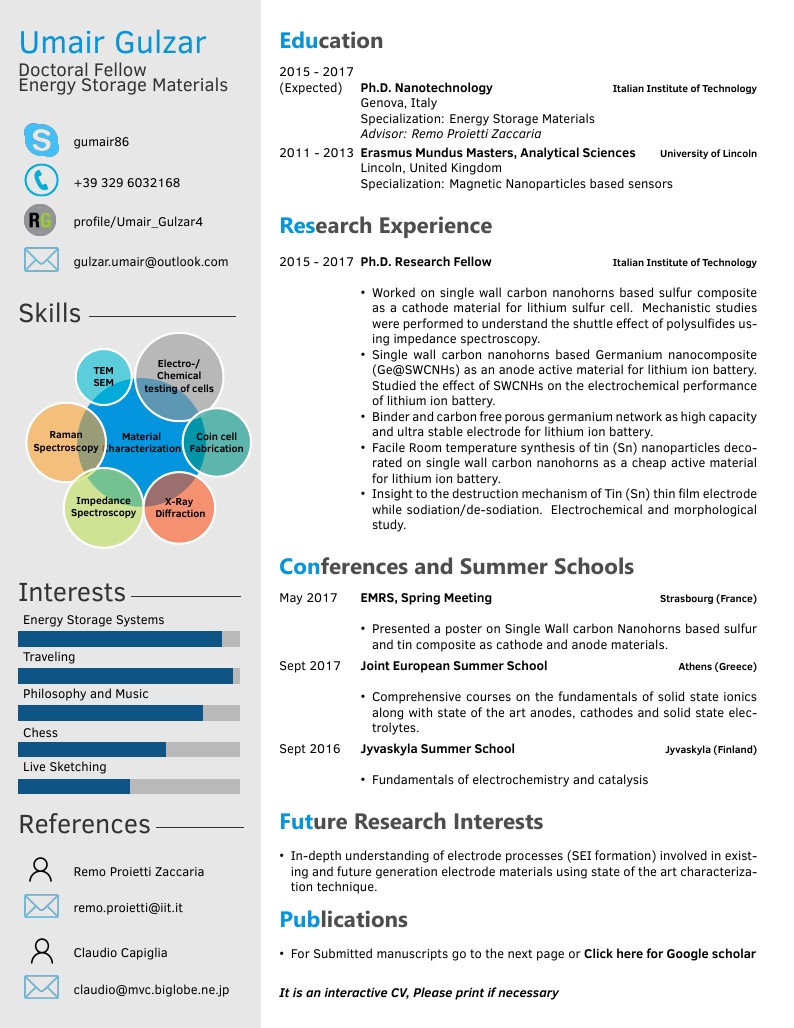
Umair Gulzar's CV
In this paper we discuss how to price American, European and Asian options using a geometric Brownian motion model for stock price. We investigate the analytic solution for Black-Scholes differential equation for European options and consider numerical methods for approximating the price of other types of options. These numerical methods include Monte Carlo, binomial trees, trinomial trees and finite difference methods. We conclude our discussion with an investigation of how these methods perform with respect to the changes in different Greeks. Further analysing how the value of a certain Greeks affect the price of a given option.
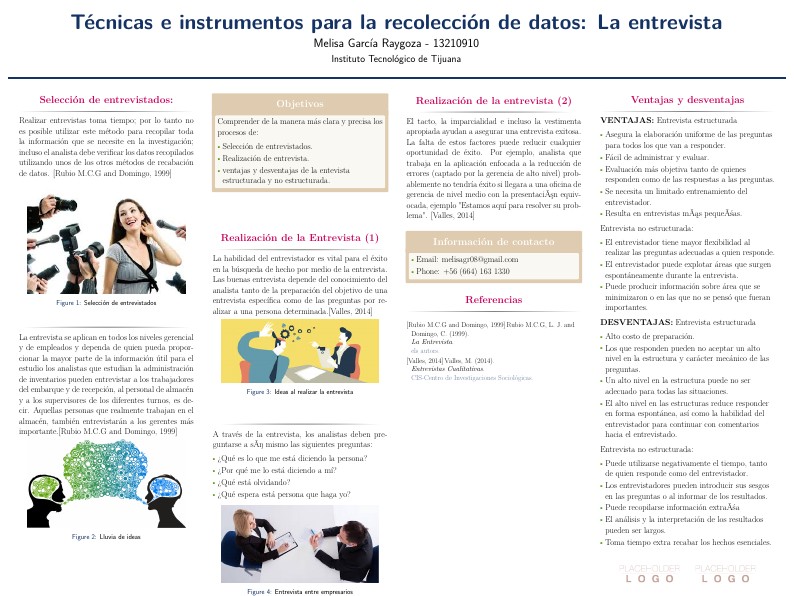
Realizar entrevistas toma tiempo; por lo tanto no es posible utilizar este método para recopilar toda la información que se necesite en la investigación; incluso el analista debe verificar los datos recopilados utilizando unos de los otros métodos de recabación de dato
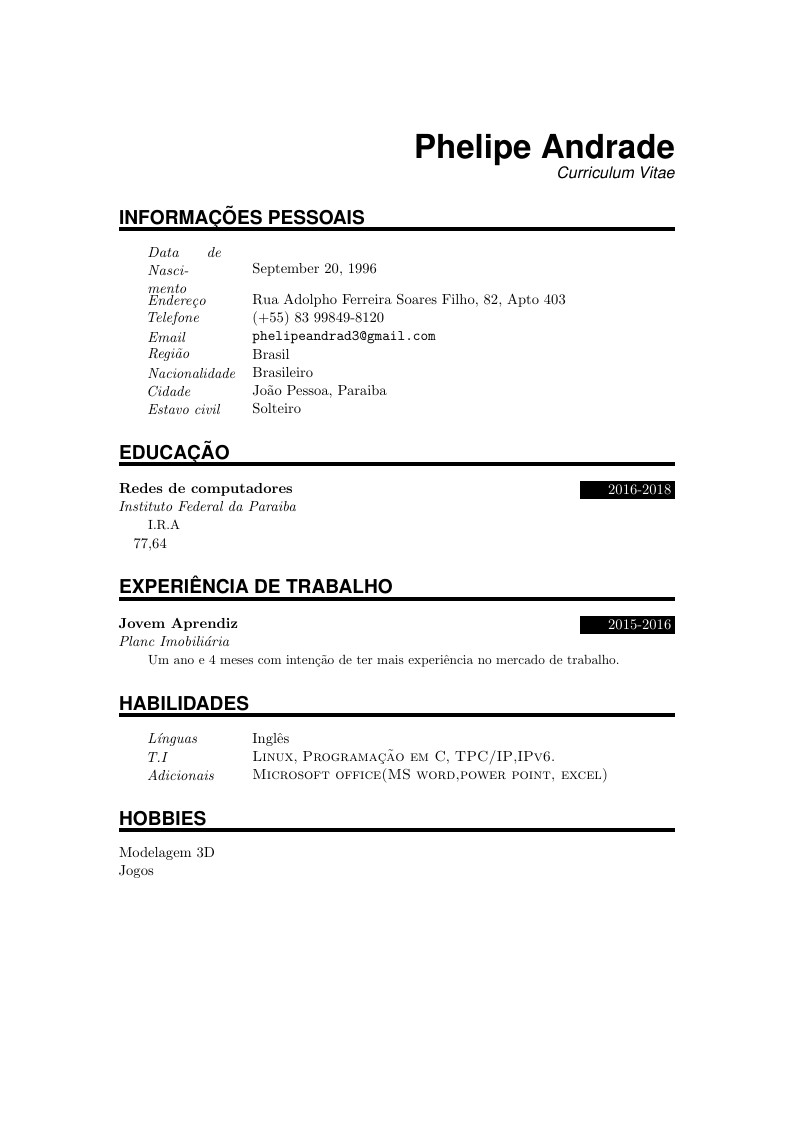
Phelipe Andrade's Curriculum Vitae
Rapport du Projet Personnel en Humanités de Kévin Bulmé ayant pour sujet l'étude des bienfaits sociaux des jeux vidéo sur les personnes et la société.

Leandro Aurélio's CV
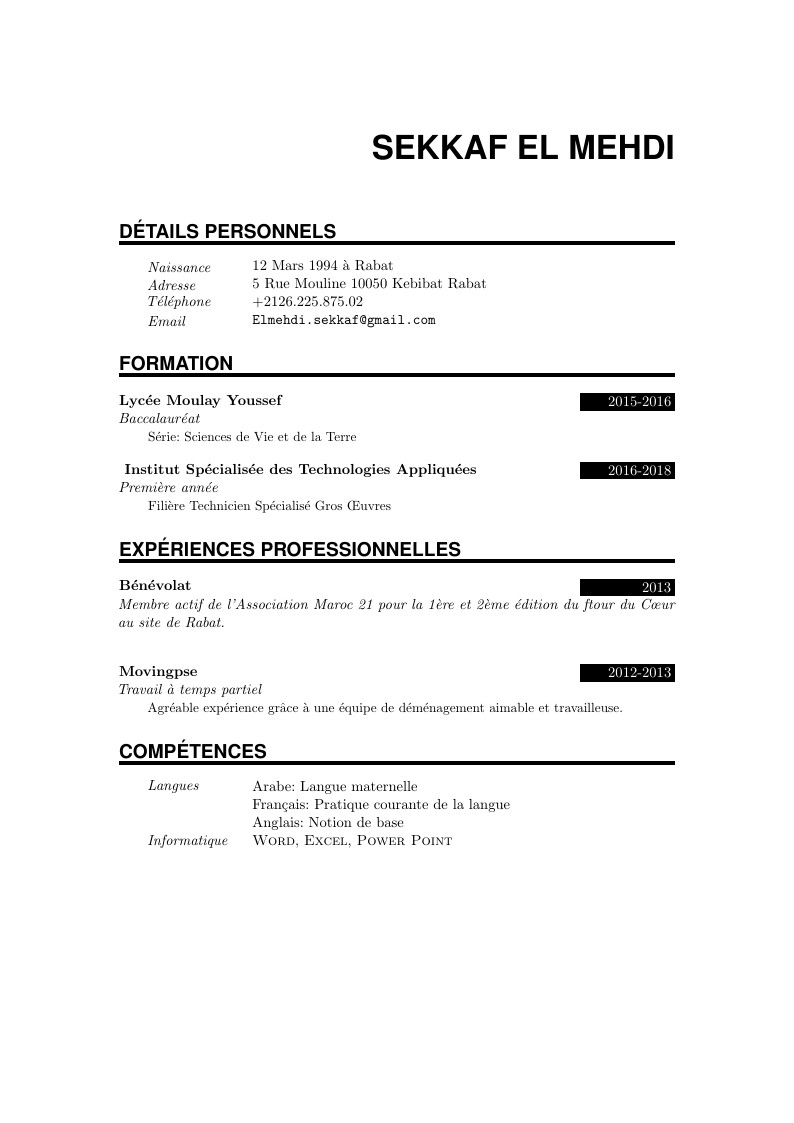
Sekkaf el MehdiI's CV