Overleaf 模板库社区文章 — Recent
论文、演示文稿、报告等,以 LaTeX 编写并由我们的社区发布。

Análisis de propiedades físicas y químicas de alcoholes, fenoles y éteres
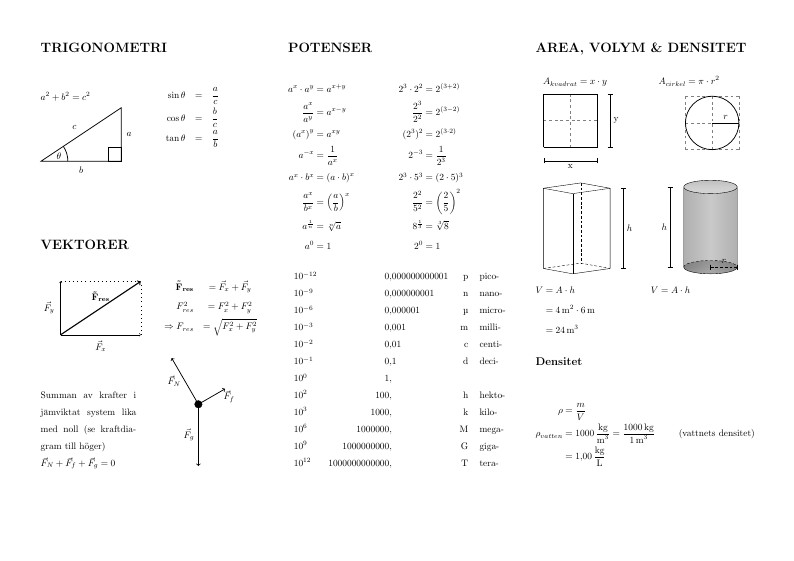
Formelsamling för fysik 1a av Jonas Vasur. Påbörjades på Mediagymnasiet (Nacka Strand), våren 2014.
Digital publishing unarguably has brought about many advantages for the dissemination of research findings. The distribution of research papers --- a format which has been used to present original data during the past 350 years --- has become faster, more affordable, longer lasting and content can be customised by the reader as publications can be assessed individually. Yet, these are incremental innovations --- a pdf remains a linear narrative, contextualised in a manner that demands human interpretation. This fundamental and largely unchanged workflow often leads to suboptimal presentation of data within publications or even omission of making data publicly available. In addition, the unique potentials of digital technologies in terms of enhancing, curating and commenting content are barely being tapped. We will discuss the impact of collaborative and dynamic authoring and publishing technologies and contemplate on what we think of as scholarly output of individual researchers. At the same time we will embark on our own collaborative authoring project and produce live session notes using writelatex.com --- everyone’s input is more than welcome!